CompuData Solutions, LLC © All rights reserved 2022.
We have clients that have been with us for over 20 years. That says a lot about of quality of work and customer service.
We perform new installations, upgrades and service and repair existing ones. The scope of our work covers security cameras, phone systems, file servers and desktops and all types of low voltage cable installations.
Contact Us and see what we can do for you.








Control who accesses your business — who, when and where. Have you ever lost your keys? Had a key break or wear out? Lost track of who has copies of the keys? Gone trough the trouble of re-keying doors?
It’s too easy for keys to end up lost or in the wrong hands. And when you have a business requiring restricted entry points, controlling access becomes even harder. With the sophisticated electronics in today's access control systems, you have total control over who has access to your building.
When access control is paired with our monitored security and video surveillance you are 100% in charge.

Access Control
Who has Access to the Premises
Anyone from visitors to employees, it’s important to control who accesses a secured space. We provide multiple ways for the intruder to prove identity before they are granted access. This is all controlled and programmed electronically to restrict or allow various levels of access.
What time periods they have access
Many businesses have employees who need access to buildings during non-
Point of Entry
Access control systems enable you to determine which individuals are allowed to open specific points of entry into your business. This is especially critical in hazardous, high-
Authentication Methods
You can choose from different access credentials types to increase security and reasonableness. There are many options which include cards with a photo ID and or company logo, key fobs, and various biometric credentials (fingerprints, hand vein geometry, retinal scans, etc.).


 Card Readers
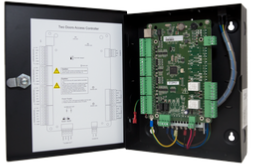
Door Controllers
Card Readers
Door Controllers
| Service Ticket |
| Card Readers |
| Door Controllers |
| Bullet Cameras |
| Network Video Recorder |
| PTZ Cameras |
| Turret Cameras |
| Database to Fillable PDF |
| Gate Controller |
| MS Access Development |
| Network Documentation |
| PassGen |
| Sample Forms |
| Authorization Form |
| Network Instalation Work Sheet |
| Router Instalation |
| Quote |
| Shipping Search |